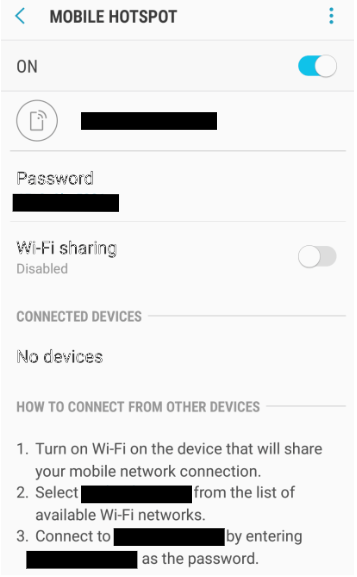
![Architecture of Mobile database security [1] From Fig. 1, it can be... | Download Scientific Diagram Architecture of Mobile database security [1] From Fig. 1, it can be... | Download Scientific Diagram](https://www.researchgate.net/publication/322465819/figure/fig1/AS:582255156142080@1515831855515/Architecture-of-Mobile-database-security-1-From-Fig-1-it-can-be-seen-that-security-is.png)
Architecture of Mobile database security [1] From Fig. 1, it can be... | Download Scientific Diagram

Cyber Security and Mobile Device Management - Cyberhunter Cyber Security | Network Security, Cloud Security & Website Security | Penetration Testing | Vulnerability Assessments | Threat Hunting







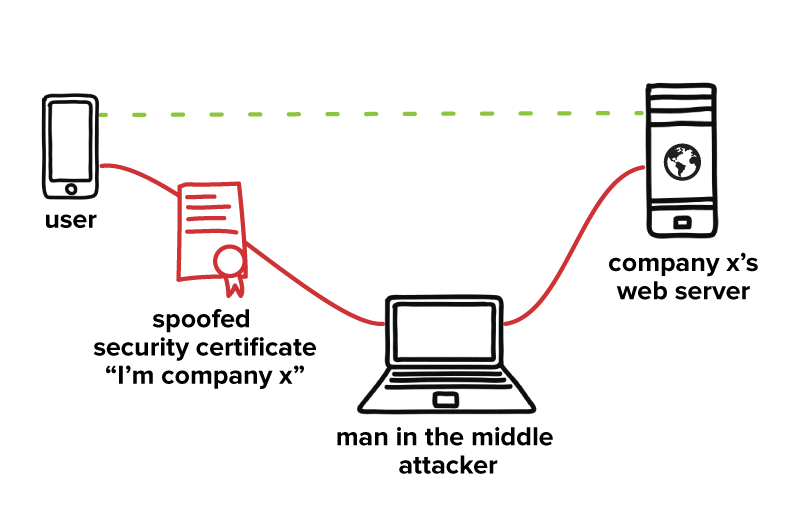


![How to find a network security key [5 devices] | NordVPN How to find a network security key [5 devices] | NordVPN](https://nordvpn.com/wp-content/uploads/blog-network-security-key-ios-1.png)